iGPT vs Threat Watch
Side-by-side comparison to help you choose the right product.
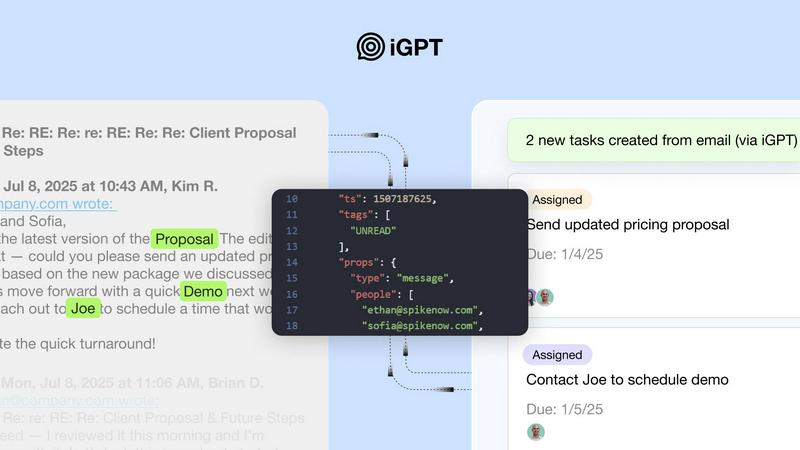
iGPT transforms email conversations into trusted, context-aware insights for seamless enterprise workflows and AI.
Last updated: March 1, 2026
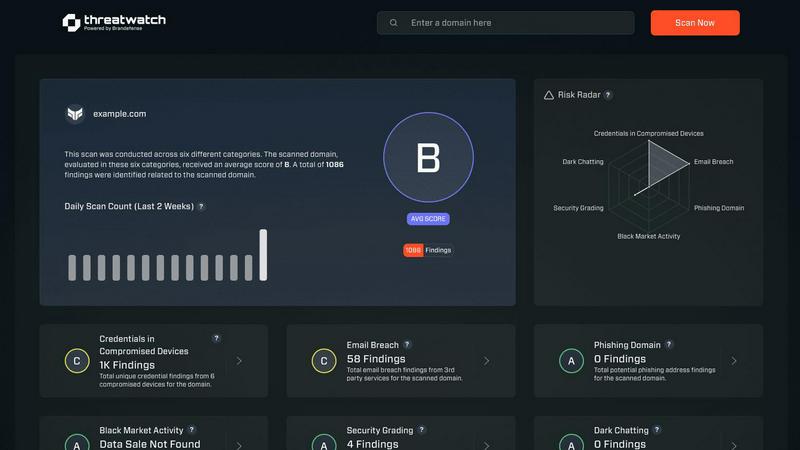
Threat Watch
Begin your journey to digital safety by instantly uncovering your cybersecurity health and risks.
Last updated: March 1, 2026
Visual Comparison
iGPT
Threat Watch
Feature Comparison
iGPT
Immediate Integration
iGPT provides an SDK and live playground that allows developers to test requests and responses effortlessly. This immediate integration ensures that teams can quickly adapt and utilize the API without extensive setup time.
Contextual Responses
With iGPT, responses are not just generated; they are crafted with context in mind. This feature guarantees that users receive answers that are ready for reasoning and automation, complete with citations to the original source material.
Hybrid Retrieval
The API employs a hybrid approach to data retrieval, combining semantic understanding with keyword searches and filters. This ensures that results are not only accurate but also contextually relevant, streamlining the information retrieval process in one seamless call.
Continuous Data Indexing
iGPT ensures that all data remains current and accurate through continuous data indexing. This feature allows new emails and attachments to be indexed instantly, guaranteeing that AI agents always have access to the latest information for decision-making.
Threat Watch
Comprehensive Cyber Health Scan
Embark on your security journey with a single, powerful command. Our fast and free initial scan acts as your first reconnaissance, mapping the landscape of your digital vulnerabilities. It evaluates critical security categories to provide an immediate, high-level view of your exposure, setting the stage for deeper exploration and remediation. This foundational insight is the crucial first step in understanding where your defenses need fortification.
Real-Time Threat Intelligence Dashboard
Navigate the ever-shifting threat landscape with a dynamic, centralized command center. This dashboard continuously aggregates and analyzes data from global sources, including dark web forums and breach databases. It translates complex threat feeds into clear, visual alerts about compromised credentials, phishing campaigns, and breached accounts related to your domain, ensuring you're always looking ahead, not in the rearview mirror.
Automated Exposure Monitoring
Set your course and let Threat Watch keep a steady watch on the horizon. This feature provides continuous, automated surveillance of your digital assets. It tirelessly scans for new exposures, such as employee credentials appearing in fresh data dumps or corporate emails targeted by phishing schemes, sending you prompt notifications so you can adjust your sails before the wind becomes a gale.
Proactive Risk Prioritization & Reporting
Not all warnings signal the same level of danger. Threat Watch acts as your seasoned navigator, helping you distinguish between distant squalls and imminent hurricanes. It analyzes detected threats based on severity and context, prioritizing risks so your team knows exactly where to focus their efforts first. Detailed, narrative-driven reports then help you communicate the journey's status and necessary actions to stakeholders effectively.
Use Cases
iGPT
Email Assistants
Leverage iGPT to build intelligent agents that can draft, prioritize, and act on emails with complete context. This capability enables teams to manage their communications more efficiently, reducing response times and improving overall productivity.
Workflow Automation
Transform email threads into actionable tasks, deadlines, and approvals with iGPT. This feature allows organizations to automate workflows effectively, ensuring that nothing falls through the cracks and that projects progress smoothly.
Support Copilots
Utilize iGPT to reconstruct customer narratives from extensive email chains, attachments, and tone shifts. This comprehensive understanding of customer interactions empowers support teams to address issues promptly and accurately.
Insights from Attachments
iGPT excels at extracting meaningful insights from attachments, summarizing critical documents such as invoices and contracts in the context of email threads. This functionality helps teams make informed decisions based on complete information.
Threat Watch
For IT Security Teams: Gaining Operational Clarity
Security analysts often feel buried in alerts, struggling to separate signal from noise. Threat Watch streamlines their voyage by consolidating intelligence into a single pane of glass. It empowers them to move from a reactive firefighting stance to a strategic, proactive defense, efficiently investigating leads on compromised accounts and mitigating risks before they escalate into full-blown incidents.
For Executive Leadership: Charting the Strategic Course
Leaders need to understand the organization's cyber risk in business terms. Threat Watch provides executives with clear, concise reports that translate technical vulnerabilities into narrative insights about potential business impact. This enables informed decision-making on security investments and helps foster a company-wide culture of security awareness from the top down.
For Compliance Officers: Navigating Regulatory Waters
Many industries require proof of diligent security monitoring and breach disclosure processes. Threat Watch serves as a vital logbook, providing documented, continuous oversight of digital exposures. This audit trail demonstrates proactive risk management efforts, aiding in compliance with frameworks like GDPR, HIPAA, or PCI-DSS by showing a committed journey towards data protection.
For Small Business Owners: Building a Resilient Foundation
Smaller ventures often embark on their digital journey without a dedicated security crew. Threat Watch acts as their essential first mate, offering enterprise-grade threat intelligence in an accessible format. It demystifies cybersecurity, allowing them to proactively monitor for stolen credentials or phishing attempts targeting their brand, building resilience without needing a vast in-house armada.
Overview
About iGPT
Imagine harnessing the true potential of your email communications. iGPT is an advanced Email Intelligence API meticulously crafted for the modern enterprise, unlocking a world where AI agents engage deeply with the complexities of email. This powerful tool acts as a secure gateway, transforming lengthy email threads and hidden attachments into actionable insights. iGPT is designed for developers and enterprises seeking to streamline workflows and enhance decision-making processes. With its remarkable ability to parse, index, and interpret communication data seamlessly, iGPT alleviates the significant engineering burden traditionally associated with email data management. A simple, natural language API call facilitates everything from real-time data ingestion to context shaping, allowing teams to craft reliable AI agents capable of discerning the nuances of deals, extracting action items, and identifying risks within customer interactions. Operating under stringent security measures, including end-to-end encryption and detailed audit trails, iGPT not only accesses your data but truly comprehends its intricacies, turning communication chaos into a strategic asset that drives business growth.
About Threat Watch
Imagine navigating a vast, shadowy ocean where unseen dangers lurk beneath every digital wave. For modern organizations, this is the reality of cybersecurity—a constant, exhausting voyage through threats that can surface without warning, threatening to breach your hull and sink your operations. Threat Watch is your dedicated lookout in the crow's nest, a vigilant partner illuminating the dark waters. It is a cutting-edge cybersecurity intelligence platform designed for the journey of every business, from nimble startups to established enterprises, who understand that true security is not a destination but an ongoing expedition. Its core mission is to transform overwhelming threat data into a clear, actionable map. By providing a comprehensive, real-time assessment of your critical security posture—scanning for compromised credentials, breached accounts, phishing addresses, and dark web exposures—Threat Watch empowers your crew. It gives you the insights to not just react to storms, but to chart a proactive course around them, fostering a resilient culture of awareness and swift response. This is more than a tool; it's your compass towards enduring cyber health.
Frequently Asked Questions
iGPT FAQ
What types of data can iGPT process?
iGPT can process a wide variety of email data, including lengthy threads, attachments like PDFs and spreadsheets, and metadata associated with communications. This versatility allows it to provide context-aware insights across different formats.
How does iGPT ensure security and privacy?
iGPT prioritizes security with features like zero data retention, role-based access control, and comprehensive audit trails. User data is never used for model training, ensuring that sensitive information remains protected at all times.
Can iGPT integrate with existing systems?
Yes, iGPT is designed for easy integration with existing systems through its SDK and unified API endpoint. This flexibility allows businesses to implement iGPT without extensive modifications to their current infrastructure.
How does iGPT handle real-time data updates?
iGPT features continuous data indexing, which means it can instantly index new emails and attachments as they arrive. This ensures that AI agents always have access to the most current information for accurate decision-making.
Threat Watch FAQ
How does the free scan work, and what do I get?
Initiating your free scan is the first step of the journey. You simply provide your business domain or key email addresses. Threat Watch then scours its extensive intelligence databases and dark web sources for any associated compromises, breaches, or phishing records. You receive a summarized report detailing found exposures across key categories, giving you a clear starting point to assess your cyber health without any commitment.
What makes Threat Watch different from a standard antivirus?
Think of antivirus as the hull of your ship—it's essential for keeping out known, immediate threats. Threat Watch, however, is your lookout and navigator. It operates beyond your perimeter, scanning the external digital ocean for intelligence on stolen credentials, breached third-party vendors, and phishing campaigns that haven't reached your shore yet. It's about proactive intelligence, not just reactive defense.
Is Threat Watch suitable for a company without a dedicated IT team?
Absolutely. Threat Watch is designed to guide voyagers of all experience levels. The platform presents findings in a clear, narrative-driven dashboard that prioritizes risks and suggests actionable steps. This empowers business owners or office managers to understand their exposure and take simple, decisive actions like enforcing password changes or alerting their team to a phishing campaign.
How often is the threat intelligence updated?
Our intelligence is a living, breathing map of the digital seas, updated in real-time. We employ automated systems that continuously ingest data from a vast array of global sources, including dark web monitoring, paste sites, hacker forums, and breach databases. This ensures the alerts and insights you see reflect the very latest discoveries, keeping you informed of new dangers as they emerge.
Alternatives
iGPT Alternatives
iGPT is an advanced Email Intelligence API designed for enterprises, allowing AI agents to extract deep insights from the chaotic world of email communications. By transforming complex threads and attachments into actionable intelligence, iGPT provides a unified approach to understanding context in business interactions. It caters primarily to developers and organizations seeking to streamline their workflows and enhance AI capabilities. Users often seek alternatives to iGPT for various reasons, including budget considerations, specific feature requirements, or compatibility with existing platforms. When exploring options, it is essential to prioritize solutions that offer robust context understanding, ease of integration, and a secure environment for handling sensitive communication data. The goal should be to find an alternative that aligns with both current needs and future growth.
Threat Watch Alternatives
Threat Watch is a cybersecurity intelligence platform designed to provide businesses with a clear, real-time picture of their digital security health. It falls into the broader category of business intelligence tools, specifically those focused on proactive threat exposure management. By automating risk assessments and monitoring critical areas like compromised credentials and dark web activity, it helps organizations move from a reactive to a proactive security stance. Users often explore alternatives for various reasons. A company's journey might require a different feature mix, a more tailored pricing model for their budget, or deeper integration with their existing tech stack. The specific needs of a growing startup differ from those of a large enterprise, making the search for the right tool a personal and strategic decision. When evaluating other options on your cybersecurity journey, focus on the core capabilities that matter most to your path. Consider the depth of monitoring, the speed and clarity of insights, and how seamlessly a solution fits into your team's daily workflow. The goal is to find a partner that not only identifies threats but empowers your team with actionable intelligence to build a resilient digital future.
